今天给本博客系统更新了简易的访问日志
发表于:2017-12-04 23:55:37 分类:开发杂记 阅读:720次
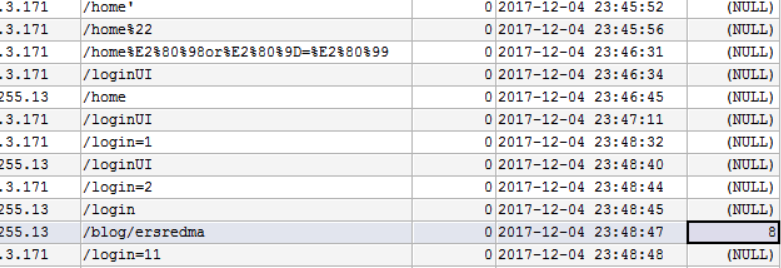
 一点点内容,折腾了一晚上。
一点点内容,折腾了一晚上。
用的filter,把之前的拦截器丢了,因为拦截器不拦截404访问。
上代码:
package top.ersredma.blog.interceptor;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.context.ApplicationContext;
import org.springframework.web.context.support.WebApplicationContextUtils;
import top.ersredma.blog.bean.ActLogs;
import top.ersredma.blog.bean.User;
import top.ersredma.blog.service.ActLogsService;
import top.ersredma.blog.utils.AppUtils;
import top.ersredma.blog.utils.OptionFiles;
import javax.servlet.*;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import javax.servlet.http.HttpSession;
import java.io.IOException;
import java.util.Date;
import java.util.concurrent.ConcurrentHashMap;
/**
* Created by ersredma on 2017/12/3.
*/
public class LogsFilter implements Filter {
private ActLogsService actLogsService;
private ActLogs logs;
private HttpServletRequest request;
private ConcurrentHashMap<String,String> coreMap=new ConcurrentHashMap<String,String>(50);
ConcurrentHashMap<String, Long> BlankMap=null;
@Override
public void init(FilterConfig filterConfig) throws ServletException {
ServletContext context = filterConfig.getServletContext();
ApplicationContext ctx = WebApplicationContextUtils.getWebApplicationContext(context);
actLogsService = (ActLogsService) ctx.getBean("actLogsService");
}
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
request= (HttpServletRequest) servletRequest;
HttpServletResponse response= (HttpServletResponse) servletResponse;
String url = request.getRequestURI().toString();
String ip=getIpAddr(request);
logs=new ActLogs();
logs.setIp(ip);
String timeNow = AppUtils.formatDate(new Date(), "yyyy-MM-dd HH:mm:ss");
logs.setTime(timeNow);
if(url.contains("/images/")||url.contains("/css/")||url.contains("/layer/")||url.contains("/js/")||url.contains("/upload/")||url.contains("validatecode.jsp")){
//logs.setRetype(ActLogs.LOG_STATUS_STATIC);
filterChain.doFilter(request,response);
}else{
User user=null;
if(access(ip,System.currentTimeMillis(),url)){
HttpSession session=request.getSession();
user=(User)session.getAttribute("USER");
if(url.contains("/mng/")){
if(user==null){
response.sendRedirect("/loginUI");
}else{
filterChain.doFilter(request,response);
}
}else{
filterChain.doFilter(request,response);
}
}
logs.setUserId(user==null?null:user.getId());
logs.setUri(url);
actLogsService.createlog(logs);
}
}
@Override
public void destroy() {
}
//获得客户端真实IP地址的方法二:
private String getIpAddr(HttpServletRequest request) {
String ip = request.getHeader("x-forwarded-for");
if(ip == null || ip.length() == 0 || "unknown".equalsIgnoreCase(ip)) {
ip = request.getHeader("Proxy-Client-IP");
}
if(ip == null || ip.length() == 0 || "unknown".equalsIgnoreCase(ip)) {
ip = request.getHeader("WL-Proxy-Client-IP");
}
if(ip == null || ip.length() == 0 || "unknown".equalsIgnoreCase(ip)) {
ip = request.getRemoteAddr();
}
return ip;
}
//判断是否拦截该ip
public synchronized boolean access(String ip,long time,String url){
String timeNow = AppUtils.formatDate(new Date(), "yyyy-MM-dd HH:mm:ss");
if(BlankMap==null) {
BlankMap = OptionFiles.readFile(request);
}
if(BlankMap.get(ip)!=null){
System.out.println("拒绝黑名单IP:"+ip+" url:"+url);
logs.setRetype(ActLogs.LOG_STATUS_REFUSE);
return false;
}
if(coreMap.get(ip)!=null){
String timeAndCount=coreMap.get(ip);
String[] arrss=timeAndCount.split("#");
if(Integer.parseInt(arrss[1])>=10){
System.out.println("拒绝超过10次危险访问IP:"+ip+" "+timeNow+" url:"+url);
BlankMap.put(ip,time);
System.out.println("加入危险ip到黑名单成功!"+" "+timeNow+" url:"+url);
OptionFiles.saveBlackData(BlankMap,request);
logs.setRetype(ActLogs.LOG_STATUS_REFUSE);
return false;
}else{
if(time-Long.parseLong(arrss[0])<500){
coreMap.put(ip,time+"#"+(Integer.parseInt(arrss[1])+1));
logs.setRetype(ActLogs.LOG_STATUS_RISK);
System.out.println("危险访问次数加1,ip:"+ip+" "+timeNow+" url:"+url);
}else if(time-Long.parseLong(arrss[0])>5000){
coreMap.put(ip,time+"#"+1);
logs.setRetype(ActLogs.LOG_STATUS_NORMAL);
System.out.println("正常访问,重置危险访问次数,ip:"+ip+" "+timeNow+" url:"+url);
}else{
coreMap.put(ip,time+"#"+(Integer.parseInt(arrss[1])));
logs.setRetype(ActLogs.LOG_STATUS_NORMAL);
System.out.println("正常的重复访问,ip:"+ip+" "+timeNow+" url:"+url);
}
return true;
}
}else{
logs.setRetype(ActLogs.LOG_STATUS_NORMAL);
System.out.println("正常的访问,ip:"+ip+" "+timeNow+" url:"+url);
coreMap.put(ip,time+"#"+1);
if(coreMap.size()>=50){
coreMap=new ConcurrentHashMap<String,String>(50);
}
return true;
}
}
}关键词:访问日志,Filter
